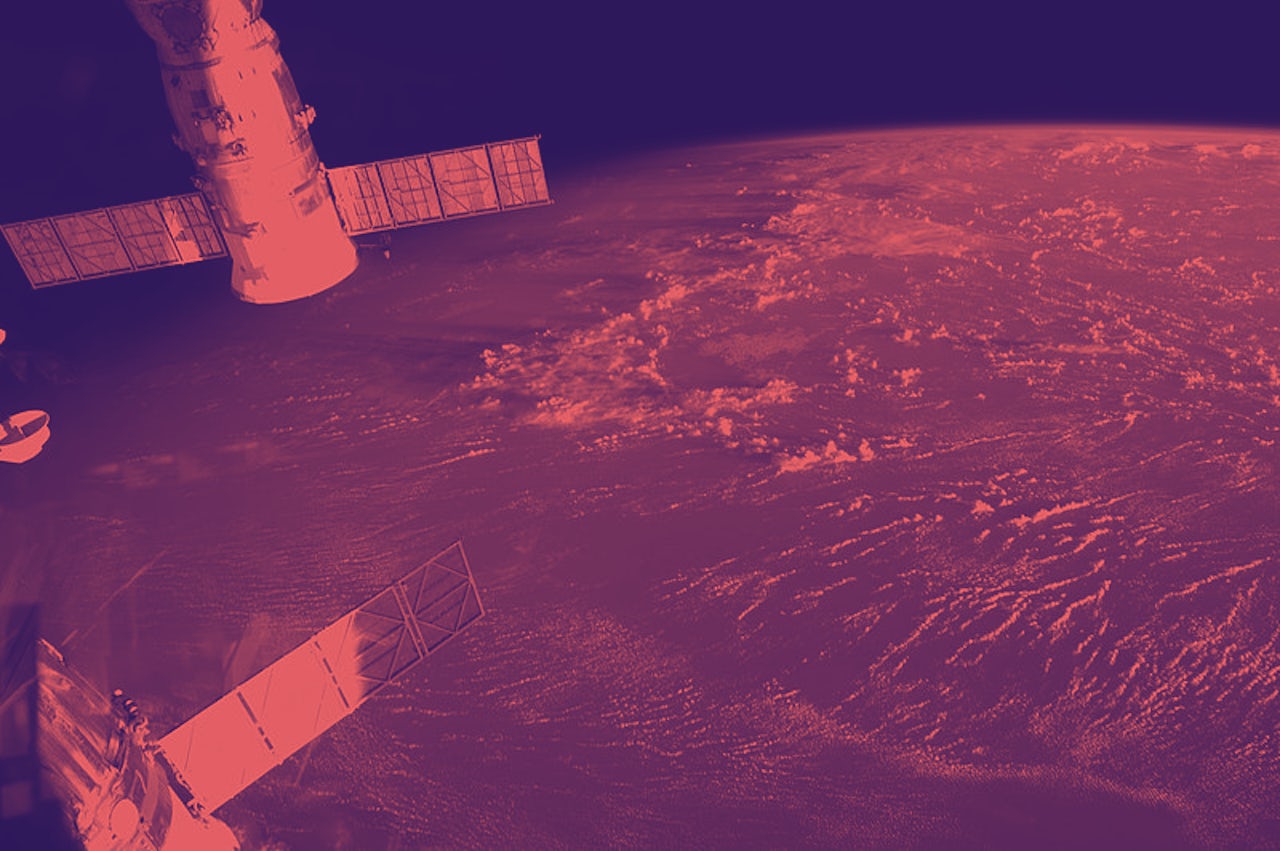
Hundreds of multi-ton liabilities—soaring faster than the speed of sound, miles above the surface of the earth—are operating on Windows-95.
They’re satellites, responsible for everything from GPS positioning, to taking weather measurements, to carrying cell signals, to providing television and internet. For the countries that own these satellites, they’re invaluable resources. Even though they’re old, it’s more expensive to take satellites down than it is to just leave them up. So they stay up.
Unfortunately, these outdated systems makes old satellites prime targets for cyber attacks.
A malicious actor could fake their IP address, which gives information about a user’s computer and its location. This person could then get access to the satellite’s computer system, and manipulate where the satellite goes or what it does. Alternatively, an actor could jam the satellite’s radio transmissions with earth, essentially disabling it.
The cost of such an attack could be huge. If a satellite doesn’t work, life-saving GPS or online information could be withheld to people on earth when they need it most. What’s worse, if part of a satellite—or an entire satellite—is knocked out of its orbit from an attack, the debris could create a domino effect and cause extreme damage to other satellites.
But scientists also can’t access the computer systems of these satellites from earth—so if something goes wrong, it’s extremely difficult to figure out who’s responsible, and there’s very little anyone can do. And with the number of satellites in space set to triple in the next several years, the stakes have never been higher.
David Fidler, a professor of law at Indiana University who has written about the intersection of cybersecurity and space policy, said in an email to The Outline that the U.S. military and private companies are now so reliant on satellite technology that they’ve become conspicuous targets. But the international community simply isn’t taking the possibility of a cyber attack in space seriously enough.
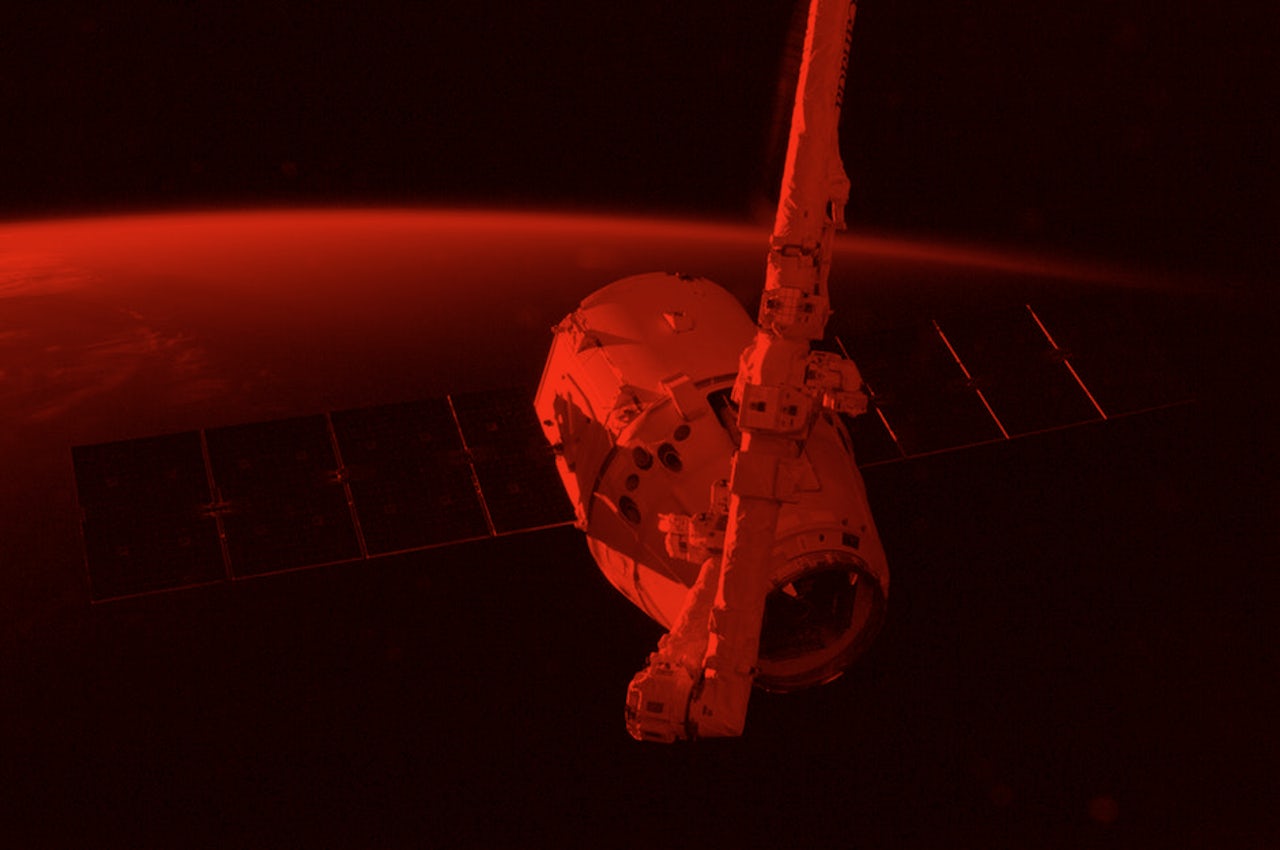
Under the National Space Council’s pro-space business guidance, the FCC recently authorized SpaceX and OneWeb to launch thousands of satellites to establish global internet. But both measures will triple the number of satellites in space in upcoming years. With the airspace so crowded, if older satellites are compromised through a cyberattack, they might move out of orbit and start crashing into other, newer satellites.
This measure in and of itself increases the risk of “space trash,” debris than can come from, among other things, broken satellites. Since space is a vacuum, a piece of trash the size of a tortilla chip could dent and severely damage a satellite. Even if a malicious actor doesn’t target new, expensive satellites, they can target weaker satellites that collide with these satellites and create even more space trash.
“We don’t need many cyber attacks to command satellites into a fatal nosedive,” Kallberg said. “Because you can’t refuel satellites, if [space trash] forces them to move in orbit, they will eventually run out of fuel. And then they’re useless.”
“Digital information and communication networks on which we depend—for public and private activities—often themselves depend on space assets to function,” Fidler said. “Adversaries will look for ways, including cyber operations, to use that dependence to their advantage.”
But outer space and cyber attacks are basically a double jeopardy of legal ambiguity. If there’s an attack, there’s no clear-cut path for countries to figure out who did it, or respond in a way that doesn’t worsen international politics on earth.
In space, it’s also even harder to figure out that there has been a cyber attack and that a rusty system hasn’t just malfunctioned. A country can’t just send a technician to the satellite to diagnose the problem. Without easy ways of getting either piece of information, the prospect of launching an attack can be very attractive. Countries such as Russia already conduct de facto state-sponsored hacking operations against the U.S.
In a scenario with such expensive damage, governments would face pressure to identify a perpetrator, and quickly. Unfortunately, governments don’t always get it right, and innocent parties take the fall.
In the event of an attack on a space asset, the 1967 Outer Space Treaty does nothing. It dictates that nations are not supposed to have war in space, since it’s an arena for the “benefits” and “interests” of mankind (but neither term is clearly defined). The treaty reads, “States shall not place nuclear weapons or other weapons of mass destruction in orbit or on celestial bodies or station them in outer space in any other manner.” Even if a crashed satellite fell to earth and caused major damage, it’s not obvious that it would violate the treaty, even though it might meet the U.S. definition of a “weapon of mass destruction.”
The one thing that is clearly defined in the treaty is government ownership. Basically, whether there’s a government satellite involved or a corporate one, the mother country is liable if or when something goes wrong.
Michael Listner, a lawyer and founder of the firm Space Law and Policy Solutions, said that this ambiguity in the Outer Space Treaty makes it wholly inadequate for addressing cyber attacks on satellites. Instead, countries would have to lean upon existing cybersecurity laws to determine a path forward.
Per Article 51 of the UN Charter, a country is justified in retaliating on another country if it’s in an act of “self-defense.” But according to Listner, “self-defense” is completely subjective, and various responses could be justified.
“Are you gonna launch a reciprocal cyber attack on one of their satellites, launch a diplomatic protest, or use some other means to retaliate?” Listner said. “All in all, you’ve gotta frame that within the context of Article 51 saying ‘this is self-defense’ so you can basically ‘justify’ whatever response you do.”
So why is it so unclear how this would all go down? According to Fidler, crafting a safe, agreed-upon response to a cyber attack on a satellite requires policymakers to have technical knowledge about satellites. “Recognition that space cybersecurity is an important issue is, actually, fairly recent,” Fidler said. “But the growing awareness comes at a time when governments are experiencing increasing difficulties in international cooperation on cyber and space issues.”
Listner said that despite grey areas in international law, states such as the U.S. likely have self-determined policies in place in the event of a theoretical cyber attack on a satellite. We just don’t know what they are.
“Chances are, they have procedures and protocols,” Listner said. “Of course, those aren’t public because we live in a competitive geopolitical environment and you don’t want your geopolitical rival knowing how you’re going to assess their response.”
Given the enormous price tag on U.S. space assets, it makes sense the U.S. is approaching the issue through multiple agencies. NASA has a Vulnerability Assessment Program (VAP) in its cybersecurity branch, designed to evaluate and minimize threats on these assets. There’s also the U.S. Cyber Command through the U.S. Army and the U.S. Cyber Forces through the Navy.
Listener said that people should take some comfort in the extent of these resources. The fact that satellites are threatened by cyberattacks doesn’t mean that a disaster scenario is inevitable. After all, countries have been launching satellites into space for over 60 years, and we haven’t witnessed a catastrophic event yet. But a no-risk scenario is basically impossible.
“I think when we’re talking about cybersecurity, there’s no such thing as 100% security,” Listner said. “You can want these systems, but we need to come to the realization that there’s always someone smart enough and clever enough to defeat them.”